- Developing An AI Vishing Model For £37.492025 was arguably the year of vishing, with the technique rapidly exploding in popularity within both red teams and real world threat actors, such as Scattered Spider. Having done some … Continue reading Developing An AI Vishing Model For £37.49
- Initial Access in 2025Having spent a lot of 2024 and 2025 focusing on initial access, I thought it might be useful to make a summary of recent public developments and techniques which have … Continue reading Initial Access in 2025
- Simulating Scattered SpiderRecently Scattered Spider (G1015) have been gathering attention from a range of attacks against UK retail, namely attacks against Marks and Spencer, Harrods and Co-Op. These have led to extensive … Continue reading Simulating Scattered Spider
- One Time Phishing Links With Caddy & AWS SES
 Caddy has long caught my attention as a much nicer alternative to Apache or Nginx which has been widely used by red teams over the years. As a bit of … Continue reading One Time Phishing Links With Caddy & AWS SES
Caddy has long caught my attention as a much nicer alternative to Apache or Nginx which has been widely used by red teams over the years. As a bit of … Continue reading One Time Phishing Links With Caddy & AWS SES - Offensive SCCM Summary
 This article aims to summarise the currently available tooling (August 2023), as well as the attack vectors which are present. My previous article covers the basics of SCCM and how … Continue reading Offensive SCCM Summary
This article aims to summarise the currently available tooling (August 2023), as well as the attack vectors which are present. My previous article covers the basics of SCCM and how … Continue reading Offensive SCCM Summary - BloodHound & Cypher Language
 A look at the more complex features of BloodHound’s Cypher query language, with several examples of how it can be used to audit an environment.
A look at the more complex features of BloodHound’s Cypher query language, with several examples of how it can be used to audit an environment. - BloodHound Basics
 A quick primer on the basics of BloodHound, the well-known Active Directory auditing tool
A quick primer on the basics of BloodHound, the well-known Active Directory auditing tool - Attacking Password Managers: LastPass
 A look into how browser based password managers such as LastPass can be attacked via various methods.
A look into how browser based password managers such as LastPass can be attacked via various methods. - RedTeamNotes: Combining Notes & Graphs!
 A quick look at a notetaking application I build whilst doing CRTO as a means of representing my notes in a directed graph to aid with red teaming
A quick look at a notetaking application I build whilst doing CRTO as a means of representing my notes in a directed graph to aid with red teaming - Digging Into Mimikatz’s lsadump And sekurlsa
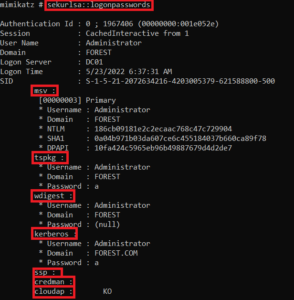 Mimikatz is a tool which has always surprised me with how many functions and features it has. In this post I dig into the lsadump and sekurlsa functions to see what all of the modules do.
Mimikatz is a tool which has always surprised me with how many functions and features it has. In this post I dig into the lsadump and sekurlsa functions to see what all of the modules do. - OffSecOps: Using Jenkins For Red Team Tooling
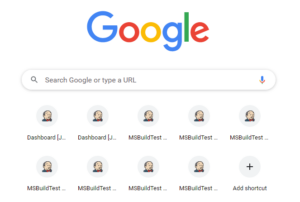 A quick look at how Jenkins can be used to automatically build payloads and tooling, based on the OffSecOps talk by Harmj0y.
A quick look at how Jenkins can be used to automatically build payloads and tooling, based on the OffSecOps talk by Harmj0y.